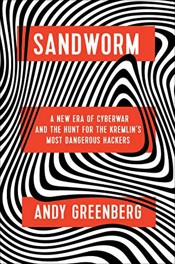
Sandworm: A New Era of Cyberwar and the Hunt for the Kremlin’s Most Dangerous Hackers
This is a story of a bunch of hacks, which the author has strung together.
The claim is that NotPetya, WannaCry, the Korean Olympic hack, etc. were all the work of the same organization – a Russian GRU hacking group nicknamed “Sandworm” (the name came from the book “Dune,” from which there were references in some of the early code).
I enjoyed the book, but there’s a lot there. The single narrative is the author’s research into a bunch of hacks, which emerge into a larger narrative of this single organization as the architect looming in the background. But in practical terms, this just means that the book is just story after story of individual hacks. It’s good, but you wonder where it’s going at some points – you need to stay aware that there’s a larger narrative to all of it.
The author does provide quite a bit of information about power grid hacking and how devastating that can be. He describes a controlled hack against a diesel generator where the hackers simply disconnect it from a power turbine, let the generator spin up very fast, then plug the output shaft back in to the slower turbine. The result is not good.
If you had any illusions that hacking was only digital, this book will teach you otherwise.
A key to reading it: remember that “Sandworm” is a group of humans. There are a lot of names in the book that refer to hacking tools and viruses. But Sandworm refers to the people that the author is looking for – the hackers behind the string of hacks.
#hacking
Book Info
- I have read this book. According to my records, I completed it on .
- A hardcover copy of this book is currently in my home library.